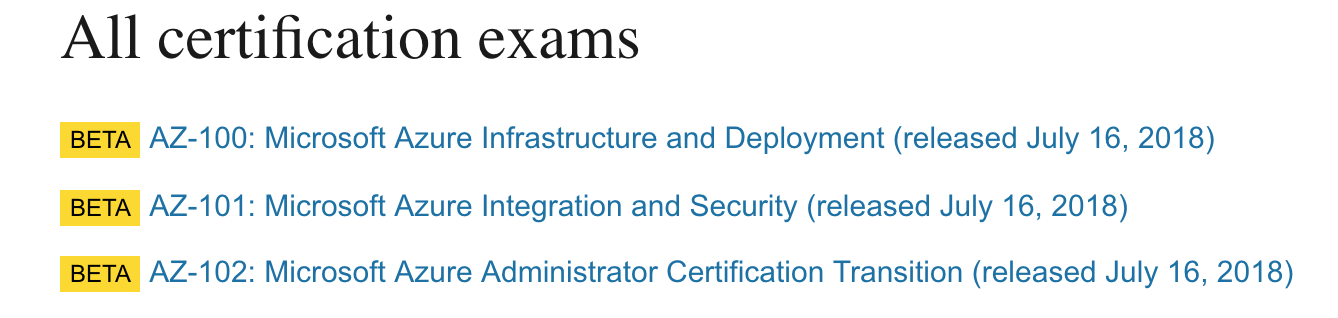
Microsoft has recently announced new certification exam tracks for Azure Administrators, Developers and Architects. Here are the line ups that should help you move your career with right certifications. The three new Microsoft Azure Certifications are: Microsoft Certified Azure Developer Microsoft Certified Azure Administrator Microsoft Certified Azure Architect These certifications would essentially split the previous […]
Read more →Category: Emerging Technologies
Emerging technologies include a variety of technologies such as educational technology, information technology, nanotechnology, biotechnology, cognitive science, psychotechnology, robotics, and artificial intelligence.
Introduction to NDepend : Static Code Analysis Tool
As a developer, you always have to take the pain of getting adapted to the best practices and coding guidelines to be followed as per the organizational or industrial standards. Easy way to ensure your coding style follows certain standard is to manually analyze your code or use a static code analyzer like FxCop, StyleCop […]
Read more →Query Routing: Intelligent Request Distribution for Cost-Efficient AI Systems
Introduction: Not all queries are equal—some need fast, cheap responses while others require deep reasoning. Query routing intelligently directs requests to the right model, index, or processing pipeline based on query characteristics. Route simple factual questions to smaller models, complex reasoning to GPT-4, and domain-specific queries to specialized indexes. This approach optimizes both cost and […]
Read more →Azure Cosmos DB – Connection Policy – Setting Connection Mode and Connection Protocol
Recently I have been trying multiple ways to optimize CosmosDb SQL.NET SDK integration calls from my web application that sits within a VNET. After carefully analyzing different options available within Cosmos Db SQL API’s have realized there are different aspects we could optimize in achieving minimal turn around time. In this article I am going […]
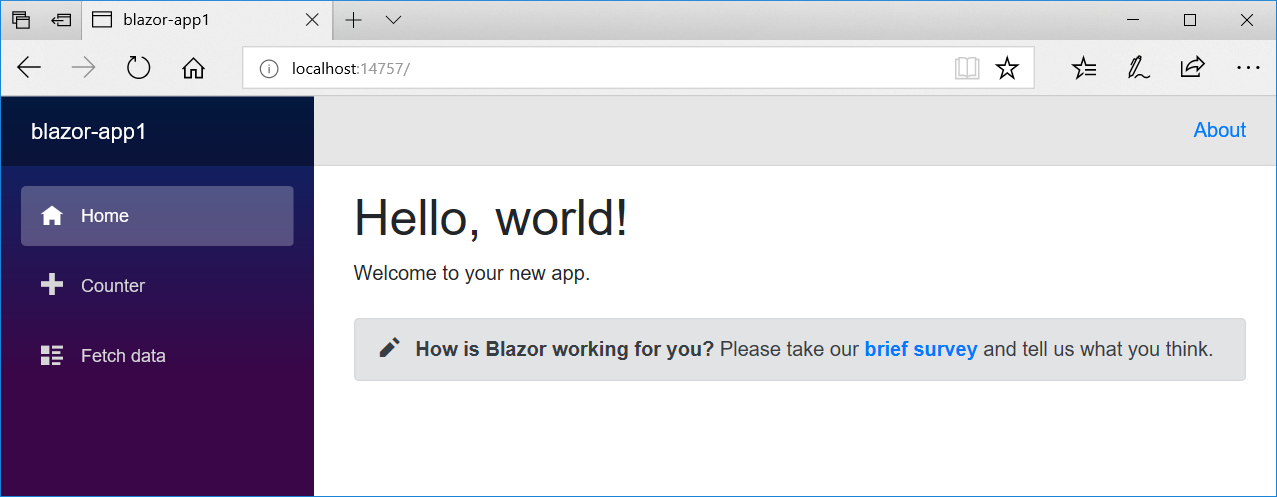
Read more →Blazer – The new experimental web framework from Microsoft
In this world of multiple Web frameworks Microsoft would not want to stop experimenting with new frameworks for Web development. Innovation is a key to Microsoft, doesn’t matter the start later than the React(Facebook) and Angular(Google) , but Microsoft has proven most of the times they are good in developing cutting edge frameworks. That’s how […]
Read more →Setting up Local NPM repository to Speedup Dev/CI Builds
As a modern day JavaScript developer working with Node.js and NPM, it has been always any developer’s case to clean up local node modules sometimes when local build is broken. It is a tedious tasks to cleanup %appData%\npm-cache to do a fresh install of all the modules again. Depending on the number of modules your […]
Read more →