Security(Cyber Security) is an essential requirement for any IoT platform or devices or end users and the communication infrastructure. In order to achieve or design best possible security solutions, to avoid some external entity or hacker gaining access to your IoT device or infrastructure, every architect or system designer should do Threat Modeling exercise. As the system is designed and architected, we can minimize the exposure to external threats to our IoT architecture.
With this article I am trying to provide you relevant bits and pieces essential for your understanding:
What is Cyber Security?
As per WhatIs.com – “Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. In a computing context, security includes both cybersecurity and physical security.”
To make it more clear and simpler – Cyber Security also known as Computer security, or IT security, is the protection of computer systems from the theft or damage to their hardware, software or information, as well as from disruption or misdirection of the services they provide. Cyber security includes controlling physical access to the hardware, as well as protecting against harm that may come via network access, data and code injection.
What is Threat Modeling?
The objective of threat modeling is to understand how an attacker might be able to compromise a system and then make sure appropriate mitigations are in place. Threat modeling forces the design team to consider mitigations as the system is designed rather than after a system is deployed. This fact is critically important, because retrofitting security defenses to a myriad of devices in the field is infeasible, error prone and will leave customers at risk.
[Content courtesy: Microsoft]
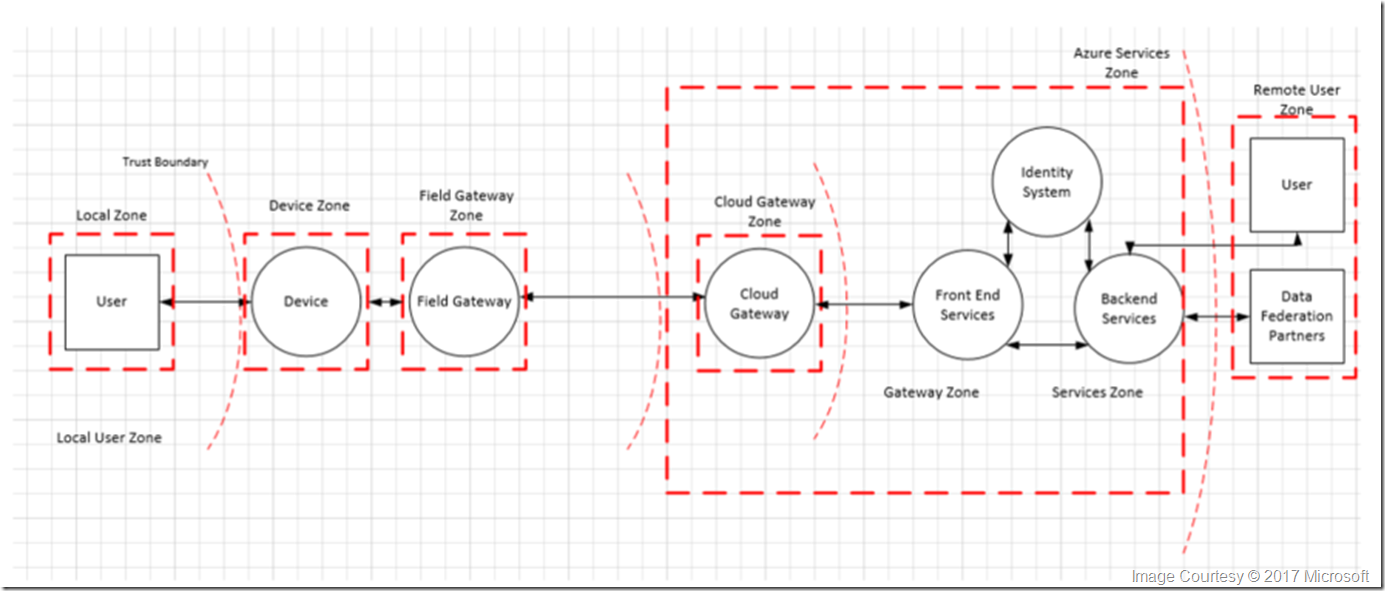
In order to optimize security best practices, it is recommended that a proposed IoT architecture be divided into several component/zones as part of the threat modeling exercise.
Relevant Important Zones for an IoT architecture :
- Device,
- Field Gateway,
- Cloud gateways, and
- Services.
Each zone is separated by a Trust Boundary, which is noted as the dotted red line in the diagram below. It represents a transition of data/information from one source to another. During this transition, the data/information could be subject to Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service and Elevation of Privilege (STRIDE).
[Content courtesy: Microsoft]
This diagram like below provides a full 360 view you any proposed solution:
Summary of important Sections/Zones:
- The Device Zone – represents a thing or device where device to device or local user physical access is possible.
- The Field Gateway Zone – Field gateway is a device/appliance (Embedded/Hardware) or some general-purpose software that runs on a Physical Server, and acts as communication enabler and potentially, as a device control system and device data processing hub.
- The Cloud Gateway Zone – Cloud gateway is a system that enables remote communication from and to devices or field gateways from several different sites across public network space, typically towards a cloud-based control and data analysis system, a federation of such systems.
- The Services Zone – A “service” is any software component or module that is interfacing with devices through a field- or cloud gateway for data collection and analysis, as well as for command and control. Services are mediators.
Once we identified threat boundaries we should be able to provide fail safe security measures each associated zones, to meet the business needs and global information exchange and data compliance standards. It is also important to design the product from the start with security in mind because understanding how an attacker might be able to compromise a system helps make sure appropriate mitigations are in place from the beginning.
In next session, we will go through Microsoft’s IoT Reference architecture and associated security measures been put together across each zones.
Additional Resources:
- Azure IoT – Security architecture
- Azure IoT – Security best practices
- Azure IoT – Secure your IoT deployment
- Azure IoT – Security from the ground up
- IoT Hub security in Control access to IoT Hub in the IoT Hub developer guide.
- SDL Threat Modeling Tool
- Microsoft Azure IoT reference architecture
Discover more from C4: Container, Code, Cloud & Context
Subscribe to get the latest posts sent to your email.